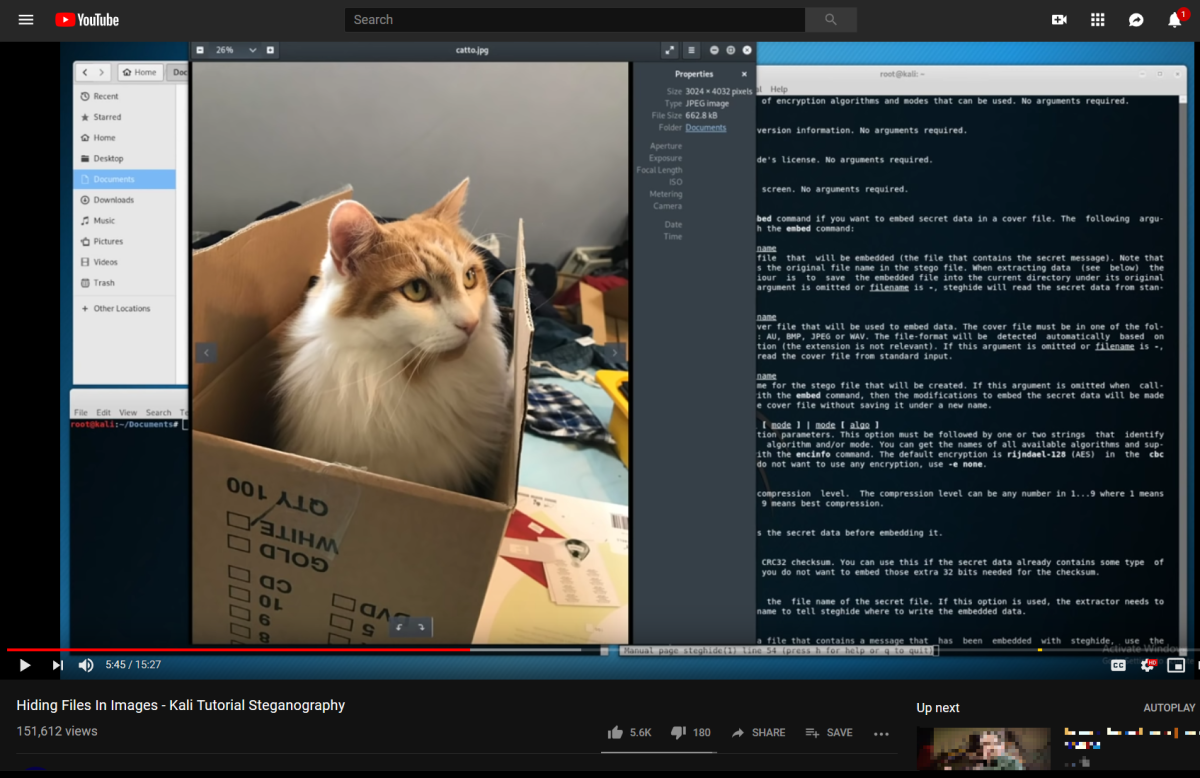
I’ve known about Stenganography for some time. And no, it’s not spelled wrong. That’s not Stenography, but Steganography. Two different things. I’ve been thinking recently about all the news items that are talking about privacy erosion and governments around the world passing or about to pass laws to break into your private messages of any kind. And then the above video popped up in my Youtube suggestions. From 2 Feb 2019 no less. Quite Recent. I’ll provide a link at the end of this post, but it’s not the main point of the video. I’m going to take that primitive program’s idea and show how it can be extended, a lot. I’m saying primitive and if you don’t believe that, watch the video. Sigh.
Steganography is:
Steganography (/ˌstɛɡəˈnɒɡrəfi/ (
listen) STEG-ə-NOG-rə-fee) is the practice of concealing a file, message, image, or video within another file, message, image, or video. The word steganography combines the Greek words steganos (στεγανός), meaning “covered, concealed, or protected”, and graphein (γράφειν) meaning “writing”.
I’m not mentioning anything the NSA does not know, but apparently the lawmakers around the world have not called in an expert who has mentioned the science of Steganography to them in their hearings for their new lawmaking regarding Privacy.
Let’s look at what’s happening to Privacy / Encryption around the world.
Governments Around the World are Trying to Shut off Encryption
And it’s not just Authoritarian governments, but Democratic ones too.
Here are some examples:
Of course they are using excuses like Crime, the “T” word, “C” “P” and other nonsense to gain the right to snoop on everything you say to anyone. I’ve used letters in quotes to avoid triggering this post as a mention of any of those obvious things, obvious to you, but not obvious to search engines, which, so far at least, are basically context free. So, what were we saying again. Oh yeah. Everybody wants to snoop on all your messages.
What’s a Solution?
So what are we to do? Well, whatever good thing we can come up with, you can bet that the smart folks employed by the bad guys have already thought of it. And the Open Source code is out there to get started. It’s all just maths, as they say in the UK. And maths can’t be outlawed or restricted, or protected. As a smart person once said:
The Net interprets censorship as damage and routes around it.
So here is an example of how the Net will route around these laws in all these countries. I’m sure I’m not inventing anything new, just reporting an idea I’ve had in Parallel with lots of other folks who are considering how to “Route Around It”.
To Build a Secure and Un-Hackable Email Service
Let’s start with the first service we need. Email.
- Use PGP or another local encryption program, on your phone or desktop or wherever, to make a private identity. Each of your “Party Members” – we’ve got to call them something, so let’s say they are trying to plan a party. Say a Baby Shower or something. So each of your Party Members does the same. So you each have a PGP Private and Public Key.
- Each of you create a QR code for your public key and pass it, in a completely secure way to your other party members. I’m gonna let you look up QR code yourself if you don’t know what that is.
- Now for the message exchange, you pick some public sites which have a lot of traffic with innocuous images. Cat Pictures, Food Pictures or whatever.
- And you agree on a way to find the other person’s images on that site. Again, you agree this in secret. And you do that in such a way that you are not communicating with each other directly. For example, We agree I’ll review Pizza places with pictures of the food, on Open Table. And you will review Sushi places on GrubHub. And so forth for all the party members. We each have anonymous posting identities on those sites. And we all know those.
- So each party member has a different triple: Review Site list, Subjects on those Sites, Anonymous Names on those sites. And we all have each other’s PGP public keys.
Sending Messages
So now to send a message, we post a review / comment on one or more of our sites with an image of anything. But the message contains a Stenganographically Encrypted / PGP encrypted message we want to send. PGP first and then Stego of course. And you probably post a few or many other images to other sites all the time too. We need to add lots of noise to each party member’s out going messages to hide any patterns. That should be easy. If you are in doubt, watch the posting patterns for anyone aged 15 – 30, and double it for good measure.
Receiving Messages with An App
To read messages, we have an app that scans a list of review sites for all of the recent comments / reviews and download many – not necessarily all of – the images associated with those comments reviews. Not just for the party members, right. No patterns that are easy followed by watching download or message traffic.
Such an app looks like many of the news scanners that are already built and are out there that look for interesting things in twitter feeds and review sites and news sites. Such an application can be built in the clear and contain nothing special. No reason to hide anything secret in this application. It has the optional feature of tossing out yesterday’s images and then saving “Today’s” images to your phone / desktop in a sort of Cache. Completely innocuous feature. It provides some way to go back and review those images with a short comment and link if you like. This is useless for our party members, but we want to make the app useful enough for anyone that we can put it in the application store and have 10s or 100’s of thousands of downloads. More noise.
Noise Upon Noise Upon Noise
You get it. The trick is to cause a lot of traffic coming to each party member from lots of random folks including lots of images. Yes, each party member is going to have a large phone bill, or maybe not. You have to decide how private and disorganized you want to look here. For sure, you don’t go to each of the review sites and look only for your party members messages. You have to add a lot of noise into the mix with lots of extraneous images to the traffic.
So we are stacking up the noise of large busy review sites, with lots of images with lots of reading of images with lots of different stuff every day, etc etc.
Actually Reading the Images
So, a Private Application, which only the Party Members have, scans the image cache for each day and tries to DE-Steganographize each of the images from only those that are associated with Party Member’s names. If they result in a message, then great, we decrypt it and we have the message. Else, it’s just noise and we toss it along with all the other pizza / sushi / cat / flowers / etc picture noise. Party members are encouraged to post often without sending messages, aren’t we? More Noise.
Encryption / Decryption Steps
Let’s look in detail at the steps to encrypt and decrypt a message. Assuming we have PGP and a Steganography library, all built together into an application.
Type in the message, including any images or diagrams you like. Any attachments etc. Whatever you like just like an email.
How much can we include? There is surely a limit to how much you can add to an image of a certain size. The Stegan-Limit let’s call it. Define this short-hand as the amount of data we can include in any image. Of course longer messages can be simply segmented and sent in packets within images. Let’s recall that some services Resize or Recompress images when uploaded. This means that the Stegan-Limit for this services will be smaller since the Stegan code will have to provide redundancy that is not lost across whatever the site does to the images. But there is plenty of time to find out what’s being done and work around it. Again, “Damage to Route Around”.
Encrypt the message or message segments with a message key and encrypt that with the PGP Private Key and Recipients Public Key[s] and provide that / those with each message segment – I’m sure that PGP can handle message segmentation, so just use the appropriate PGP library functions. No invention required.
Steganographize the message segments into the recent set of images for your postings and scatter them around in reviews comments whatever on the site or sites of your choosing.
Analysis Questions
I’m not a Steganography Expert. But let’s ask some questions:
- It is given that an encrypted message or message packet when encrypted looks like noise. There is a problem if that’s not true.
- It must not be possible to determine whether an image contains a message unless you know the key. There cannot be a way to look in the message and see a finger print that says : “Steganographic Data Hidden Here”. The whole point of this exercise is to HIDE and that signal is NOT HIDING.
- So, the Un-Steganography process reproduces a random bit stream, which we then try to Decrypt using PGP – or a minor modification of PGP. Only at this point do we have a message, or even a hint that there is a message. If we get junk back when we try to decrypt then there’s no message. Yes. I’ve been talking as if it’s 1 to 1, but PGP already solves 1 to Many, right? I mentioned PGP Public Key[s] above remember?
So, what’s this paper is trying to argue is that if these things are true, or Maths can be created to make them true, then all this nonsense about Laws to Require Privacy Breaking Back Doors is nonsense, and the folks that are already studying this problem – deep in the bowels of NSA and the Bad Guy Labs – already know this and the laws are all nonsense.
Only the bad guys and the hopefully good guys are using this technology already or will soon. This would seem to be obvious to any of us who have studied security for any length of time.
How to Crack This?
Note that this does not require any of the “Services” i.e. Review Sites, to cooperate in the act of message delivery. They can log anything they like. There is nothing to ask them for except the usage logs of the Party Members.
The whole idea of this is to hide who are the party members and what they are saying in a sea of noise. Have at it boys. Download all the logs and with something like the above rules among party members, load all of the traffic of the top 10 popular review sites and then look for patterns? Remember, the members use multiple sites, not the same sites. Once you know the party members, you can find that the set of sites overlap, but before you know the members, you are stuck, I think. It’s a many to many problem with millions of many’s and there are already millions of False Positives: That is real friends talking with each other and sharing cat pictures, and that is going to corrupt your search.
So unless the Party Members can be found in other ways before the search, then you don’t know which images to look at, and then when you do look at the images, it looks like they were taken with Noisy Mobile Phone cameras, which they were.
And they aren’t even talking with each other. All you can see is that they, among all the other stuff they see, are seeing each others images. Actually they are all downloading more images than anyone could possibly look at. But don’t we all do that? All those Ad Images that go right by? Did I see all those images in all those comments that were downloaded to my phone? Not a chance.
Other Possible Developments
Firewalls of Wherever
The great internet firewalls of wherever cannot see these things. So cat pictures will leak in and out of any of the great firewalls that are here or coming. Russia, Turkey, Iran and how many other places think they can bottle up their countries. Well the only way to do that is to cut off the bits completely, and how is banking and any business going to work in that environment? Even the leader is going to have to eat. Only North Korea can truly be cut off from the rest of the world and look at their current state? Russia? Turkey? Iran? You signing up for that? All your folks starving and your economy dependent on a large and rich neighbor [China?] keeping everything afloat? I doubt it.
We don’t need TOR or VPNs to be private. Those things are signals of attempted privacy and will be shut down. These are “damaged” and must be routed around in the new internet. Cat pictures will route around the damage. The key is to provide no “Signal” of attempted privacy.
Covert Streaming
Looks like you could make a Twitch Channel too with this technology. I’m guessing that the amount of video you can hide in another video is pretty limited. So you might get a 320p or 480p video hidden in a 1080p video for example, and it might be less obvious that you were doing that if the “Quality” of the HD video were lower. This might allow two party members to have a covert video conference while their buddy played a video game and chatted with lots of other folks. Don’t cross the streams, as they say. Sorry bad joke.
Steganographically Hidden Virtual Machine
What if you wanted to hide all this software on your computer? You can’t hide a Virtual Machine if someone looks at your drive. It’s going to be a “Signal” if someone sees a large encrypted file that is a VM of Linux or whatever OS that is running TrueCrypt or something. One huge file that’s a blob of noise? That’s going to be very suspicious. That large encrypted file on your disk and the VM software.
But what if your disk had a few 10s of GB of cat images – say for example. They might be any images really, the noisier the better. And what if there were a relatively small, but encrypted driver that hides a whole Virtual Machine hard drive Steganographically in those cat pictures? Impossible? Even with one or two high speed graphics cards to do the Steganography / Cryptography? Dual Graphics Cards are a thing now. Ask any Fortnite player. After all, with large memory RAM capacities, you don’t have to write back to the cat images in real time, use a RAM disk cache and write new data back later as the system has time. Only the last changes would be dumped back into Stego form into the images.
So, they pick up your computer and search the hard drives and voila, yes indeed you are a cat / flower / landscape / food photographer and you have 10s or 100s of GB of pictures to prove it. And some out-dated VM software that runs an old copy of Windows XP or some old Linux Distro with an ancient Console Game Emulator. Whatever. More noise. But with the right GRUB boot loader input and the right password, up comes the real Virtual Machine hidden in the Cat Pictures and away we go.
And the system runs RAID across the images so that if a bunch of them are deleted, the whole thing still works.
Good luck finding all that stuff. Because you won’t know to look for it.
Here Comes the Future
I’m sure I’m not telling anybody anything new if they have been thinking about this problem and are trained in Security and Maths. But someone needs to tell the Lawmakers the real reason that the Net is Going to Go Dark for surveillance. And it’s not because of WhatsApp and Apple’s Secure Enclave. Those laws are just going to cause these ideas or better ones like them to be completed and used.
And the other good news is that it’s possible to give a voice – secure and private – to oppressed folks everywhere. And someone will do that too.
One way to think about this whole thing is that our use of the internet has created a perfect place to hide. There is so much, and growing, noise that we no longer need TOR to create noise. We just send out our data on the sea of noise that is the modern internet in such a way that it can be found by only the right persons who want it.
Perfectly Private Communication among folks in a sea of noise where there is no privacy.
Remember:
The Net interprets censorship as damage and routes around it.
I lied. I’m not going to give you the link to the video that caused this post. You’re smart. You can find it given the above image.
:ww